7 Fundamental Ways to Repel Ransomware
Trustwave Research Reveals Cybersecurity Risks Threatening Patient Lives in Healthcare. Learn More
Get access to immediate incident response assistance.
Get access to immediate incident response assistance.
Trustwave Research Reveals Cybersecurity Risks Threatening Patient Lives in Healthcare. Learn More
Let's put aside for a moment the mega data breaches that resulted in millions of confidential customer records going out the door. If 2015 is to be remembered for one thing in the world of cybersecurity, it might be the year ransomware hit the big time.
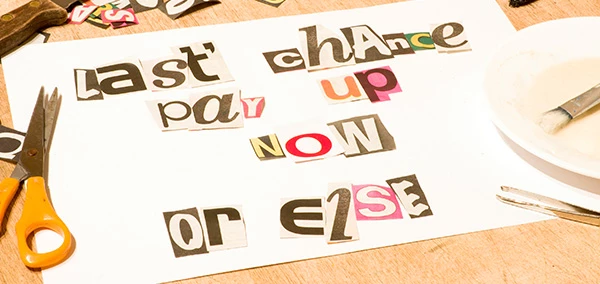
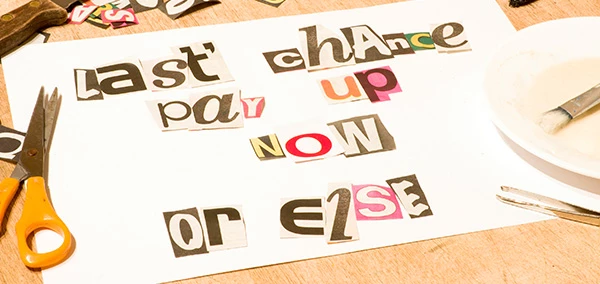
Ransomware is "kidnapping" malware that has been plaguing home users and businesses for many years, but which has significantly spiked over the past 24 to 36 months to become a hugely profitable racket for cybercriminals - and a source of great tension for IT and security professionals. The threat initially gained notoriety for its maddening ability to freeze individual keyboards and computers - usually with bogus statements from the FBI concerning child pornography - but in recent years it has evolved to encrypt sensitive data files, with the attackers the only ones holding the private keys to unlock them. The most recent strains of ransomware are going even one step further: They are being bundled with password stealers that are used to exploit weak website security.
The fraudsters won't release the key, of course, until you make a payment, usually requested in bitcoins. The going-rate is around $500, but the shakedown can stretch into the several thousands of dollars for victims - never mind the costs associated with downtime and recovery, as well as potential legal and customer-related costs. Because the attack is so crippling, many businesses end up deciding to pay the ransom - an outcome that even the FBI hasn't encouraged against. The most common ransomware family is CryptoWall, which the Internet Crime Complaint Center in the United States estimates was responsible for nearly 1,000 complaints between April 2014 and June 2015, with those victims reporting some $18 million in losses. TeslaCrypt and CBT Locker are two other families that are popular. Reveton and Chimera are still around, but somewhat outdated.
Purveyors of ransomware typically stop short of exfiltrating compromised data as we've become accustomed to with traditional data breaches. Instead, they aspire for a quick hit and an even quicker reward. Once compensated, they usually live up to their end of the bargain and release the data from their control - If they didn't, nobody would ever pay the ransom - although that's no guarantee they've abandoned their foothold in the target environment.
Ask any security expert why ransomware has become so popular and they'll give you roughly the same answer: It's not a complicated scam requiring different players handling specific tasks (as you might find in a credit card breach operation). It often results in quick cash - Trustwave researchers estimated the return on investment for ransomware attackers is a whopping 1,425 percent - and most of all, it works. The threat is often difficult to detect and even harder to remove once it has infiltrated a target, which, by the way, doesn't just include PCs, but also mobile devices (where the threat is growing fast), Linux-based systems and even medical devices.
What steps can you take to rebuff a ransomware attack? Try these seven recommendations:
This allows you to quickly recover from an incident. Be sure to regularly replicate file changes in your production environment, so your fallback point is an acceptable amount of time for your organization in case of an attack.
At the first sign of a malware infection, detach the compromised machine from the network, cutting off the attacker's control of it. However, take note that this will not stop the encryption process if it's already been initiated by the ransomware.
It's not enough to simply have anti-virus running on your desktops. You also need live anti-malware capabilities that can conduct real-time code analysis and dynamic URL categorization.
Ransomware scams tend to begin like most malware infections - with an end-user clicking or opening something malicious. Preach the importance of social engineering defense.
To complement awareness with technology, you should adopt an email security gateway that incorporates threat intelligence to effectively thwart emails that contain malicious URLs.
Malware often requires an unpatched vulnerability to run, so ensure that your entire environment is updated with the latest security fixes. Vulnerability scans and security testing help businesses identify their network-connected assets and learn how those assets are vulnerable to attack.
If you're a victim of a ransomware attack, you need to kick in incident response, which should include contacting the authorities and/or filing a complaint with IC3.
Dan Kaplan is manager of online content at Trustwave and a former IT security reporter and editor.
Trustwave is a globally recognized cybersecurity leader that reduces cyber risk and fortifies organizations against disruptive and damaging cyber threats. Our comprehensive offensive and defensive cybersecurity portfolio detects what others cannot, responds with greater speed and effectiveness, optimizes client investment, and improves security resilience. Learn more about us.
Copyright © 2025 Trustwave Holdings, Inc. All rights reserved.