Appending a malicious file to an unsuspecting file format is one of the tricks our adversaries use to evade detection. Recently, we came across an interesting email campaign employing this technique to deliver the info stealer Vidar malware. First, let’s examine the email delivery mechanism, then go on to take a closer look at the Vidar malware itself.
 Figure 1: The malicious spam message
Figure 1: The malicious spam message
The messages in this campaign have two things in common. First, the email body has similar text, which as usual, directs the recipient’s attention to the attachment.
Second, the email contains only one attachment named “request.doc”, which is actually an ISO file. ISO is a disk image file format that cybercriminals repurpose for use as a malware container. In this campaign, the ISO attachment holds two files – a Microsoft Compiled HTML Help (CHM) file “pss10r.chm” and an executable “app.exe.” Once the attacker tricks the recipient into extracting the contents of “request.doc” and then executes either one, the system can be compromised.
The CHM Loader
CHM is Microsoft Proprietary online help file format normally used for software documentation. When executed, Microsoft Help Viewer (hh.exe) loads the primary object of the CHM.
 Figure 2: The MailMarshal unpack tree of the ISO attachment
Figure 2: The MailMarshal unpack tree of the ISO attachment
As shown in Figure 2, MailMarshal supports the unpacking of ISO and CHM files. One of the objects unpacked from the CHM is the HTML file “PSSXMicrosoftSupportServices_HP05221271.htm”- the primary object that gets loaded once the CHM “pss10r.chm” is opened. This HTML has a button object which automatically triggers the silent re-execution of the CHM “pss10r.chm” with mshta.
 Figure 3: The legitimate PSS10R.CHM in Windows vs the one contained in the ISO attachment
Figure 3: The legitimate PSS10R.CHM in Windows vs the one contained in the ISO attachment
Mshta is a Windows binary used for executing HTA files. Looking at the CHM “pss10r.chm” statically, some HTML Application (HTA) code is noticeably lurking at the tail end. The appended HTA has some JavaScript that silently runs ‘app.exe’, the second file inside the ISO attachment. Note that for this loader to work, the executable must be extracted to the same directory as the CHM file.
 Figure 4: The HTA appended at the CHM Loader ‘pss10r.chm’
Figure 4: The HTA appended at the CHM Loader ‘pss10r.chm’
The Vidar Malware
The executable “app.exe” is the malware known as Vidar, which is an information stealer compiled in C++ capable of harvesting system information and data from a wide range of browsers and other applications in the system.
 Figure 5: Vidar advertised on ultrahacks.org
Figure 5: Vidar advertised on ultrahacks.org
Once executed, this malware will not proceed to its malicious routine if the computer and username of the system is JohnDoe and HAL9TH, respectively (artifacts from Windows Defender emulator), and if the following DLLs related to sandbox and AV and email scanners are loaded into the system.
api_log.dll cmdvrt64.dll snxhk.dll
avghookx.dll dir_watch.dll vmcheck.dll
avghooka.dll pstorec.dll wpespy.dll
cmdvrt32.dll sbiedll.dll
The Vidar samples we obtained, which were all version 50.3, retrieve their command and control (C&C) servers from Mastodon, an open-source social networking platform. The samples searched the following profiles and grab the C&C from the Bio section:
mastodon.social@kill5rnax
noc.social@kill6nix
 Figure 6: The Mastodon profile containing Vidar’s C&C
Figure 6: The Mastodon profile containing Vidar’s C&C
Before the stealing routine, Vidar downloads its dependencies from the C&C and saves them at C:\ProgramData. Then, it retrieves its configuration setting.
freebl3.dll
mozglue.dll
msvcp140.dll
ns33.dll
softokn3.dll
vcruntime140.dll
 Figure 7: The returned setting with 95[.]216[.]181[.]231/1149
Figure 7: The returned setting with 95[.]216[.]181[.]231/1149
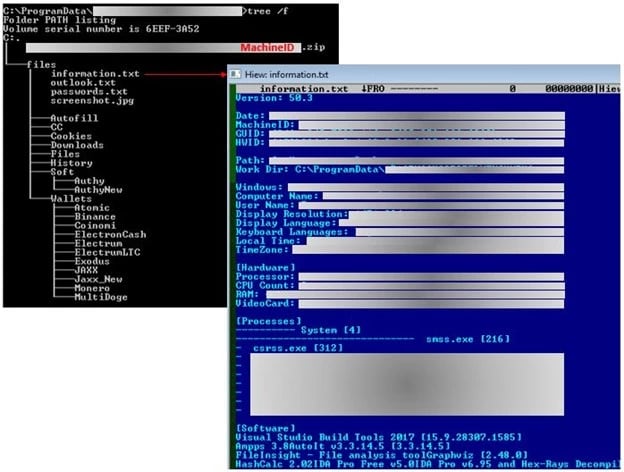
Vidar creates its own folder at C:\ProgramData. The data it collected from the infected system are saved on C:\ProgramData\<random>\files. Then, this is archived at C:\ProgramData\<random>\<machine GUID>.zip and sent to the C&C.
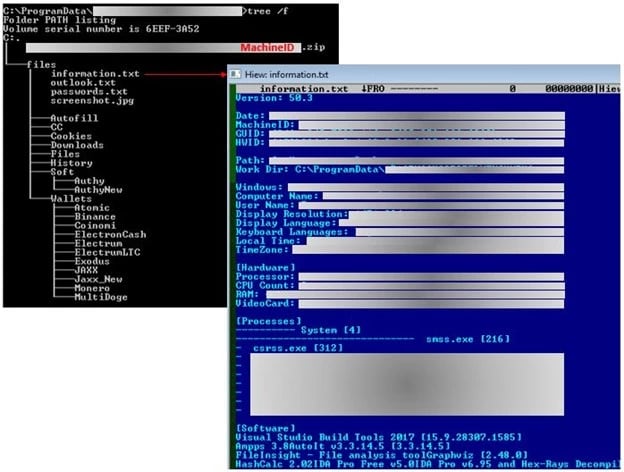 Figure 8: The folders and files created by “app.exe”
Figure 8: The folders and files created by “app.exe”
We observed in the code that in response, the C&C can send a download URL of an executable. This process can lead to another malware being installed in the system.
 Figure 9: Vidar can download and execute an executable
Figure 9: Vidar can download and execute an executable
Lastly, the files created by this threat are deleted, as well as all the DLL files in %programdata%. Below is the command used.
C:\Windows\System32\cmd.exe /c taskkill /im <Vidar executable> /f & timeout /t 6 & del /f /q \" <Vidar filepath>\" & del C:\ProgramData\*.dll & exit
IOC
request.doc (1996800 bytes)
SHA1: 4E5BC4B8CB05872721C1D4965C14D395ED0B3221
pss10r.chm ( 949858 bytes)
SHA1: EFE3E712C667CE1D61C8613D03F7EAE31782BDBF
PSSXMicrosoftSupportServices_HP05221271.htm (2710 bytes)
SHA1: 762DF02815D9E5A4D4058081D3FF479853B1348D
app.exe (674304 bytes)
SHA1: 8CB6279E76DCA6DFDEF1079CB336C0F2D69AC9D3
95[.]216[.]181[.]231 - C&C